2 Conventions
This document has adopted the following conventions for representing the framework concepts and specifying how the standards upon which the IHE IT Infrastructure Technical Framework is based should be applied.
2.1 The Generic IHE Transaction Model
Transaction descriptions are provided in Section 3. In each transaction description, the actors, the roles they play, and the transactions between them are presented as use cases.
The generic IHE transaction description includes the following components:
- Scope: a brief description of the transaction.
- Use case roles: textual definitions of the actors and their roles, with a simple diagram relating them, e.g.,:
- Referenced Standards : the standards (stating the specific parts, chapters or sections thereof) to be used for the transaction.
- Interaction Diagram : a graphical depiction of the actors and messages that support the transaction, with related processing within an actor shown as a rectangle and time progressing downward, similar to:
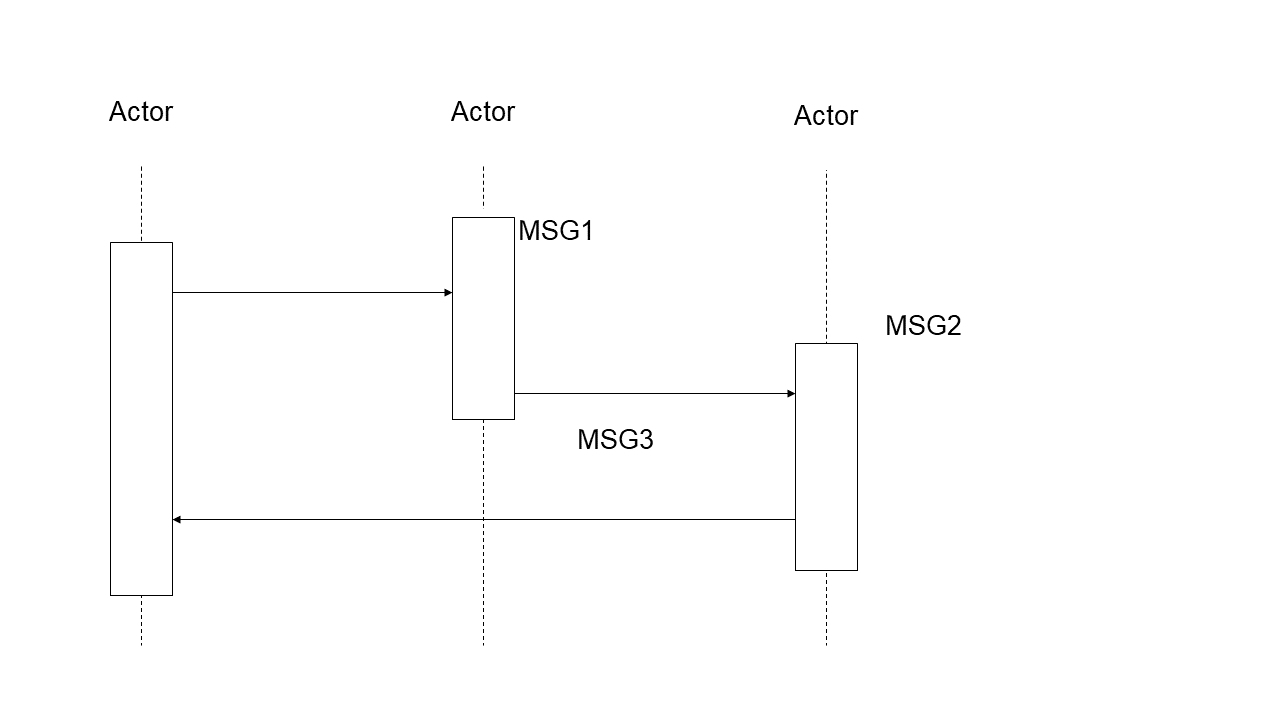
The interaction diagrams used in the IHE IT Infrastructure Technical Framework are modeled after those described in Grady Booch, James Rumbaugh, and Ivar Jacobson, The Unified Modeling Language User Guide , ISBN 0-201-57168-4. Simple acknowledgment messages are often omitted from the diagrams for brevity. One or more messages may be required to satisfy a transaction. Each message is represented as an arrow starting from the actor initiating the message.
- Message definitions : descriptions of each message involved in the transaction, the events that trigger the message, its semantics, and the actions that the message triggers in the receiver.
2.2 HL7 Profiling Conventions
See ITI TF-2: Appendix C for the HL7 profiling conventions as well as the networking implementation guidelines.
2.3 Use of Coded Entities and Coding Schemes
IHE does not produce, maintain or otherwise specify a coding scheme or other resource for controlled terminology (coded entities). Where applicable, coding schemes required by the HL7 and DICOM standards take precedence. In the cases where such resources are not explicitly identified by standards, implementations may utilize any resource (including proprietary or local) provided any licensing/copyright requirements are satisfied.
